I have used spamassassin for many years with variable levels of success.
I will tighten the rules in one place, the soammers would find a new way to deliver the spam on my server.
Last week my wife, retired her email address because she’s getting more spam than real mail.
It was the worst of the worst of it was as if my wife were a pornography addict and she never looks at that stuff.
So I analyzed the headers. Turns out spamassasin was not even processing the messages at all. They came in on localhost 127.0.0.1 and were passed straight to the amavisd virus filter.
As it turns out spamassassin treats all emails from local host as a trusted network. Well the spammers changed that fact 4 years back.
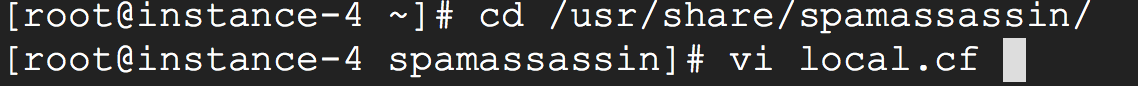
So I scoured the forums and came up with this:
The first statement tells spamassassin to check all headers regardless of what network it came from.
report_safe 1 trusts mail from trusted networks. By default 127.0.0.1 is a trusted network.
clear_trusted_networks makes sure spamassassin does not have any more so called “trusted” networks.
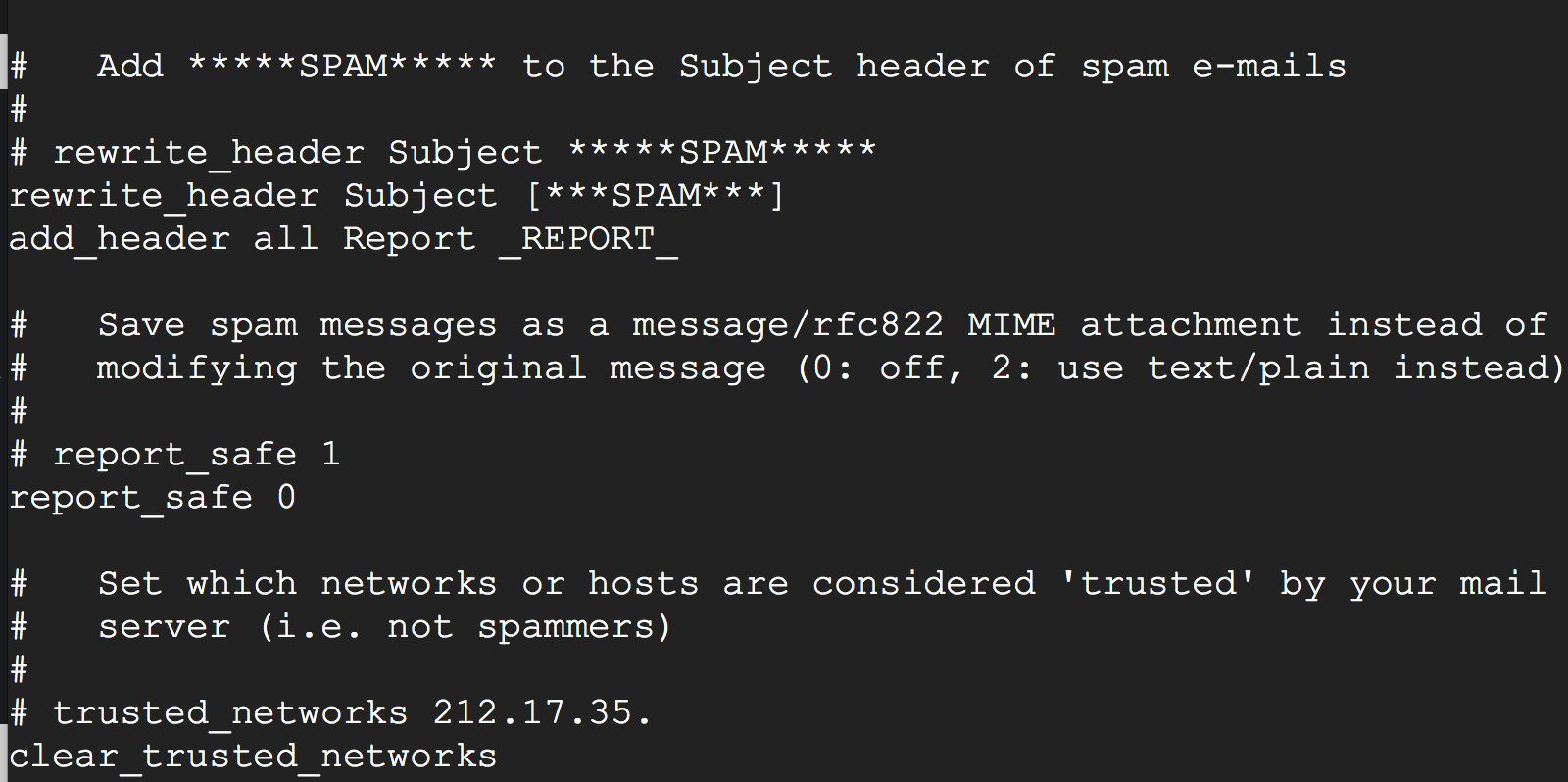
Spammers also probe and make lots of mistakes. I have configured postfix to slow them down big time.
Any error triggers a 90 second timeout. I plan to crank that up. The spammers probing manually don’t like to wait. The scripts don’t know how long to wait. This and the next change are useful in avoiding dos/denial of service attacks.
You get two errors interacting with my mail server before you disconnect. The default was 10/20.
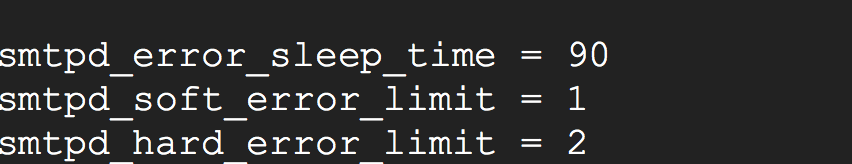
After making the first changerun:
systemctl restart spamassasin
systemctl status spamassasin -l
After the postfix main.cf change:
systemctl restart postfix
systemctl status postfix -l